Our Services
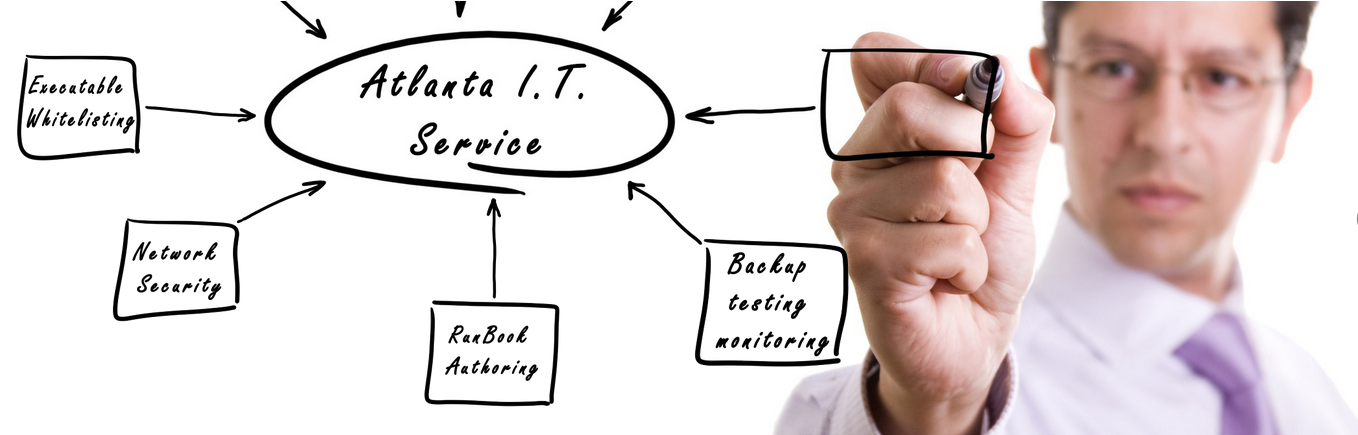
If your business is dependent on the data that it generates from day to day, you should consider speaking with us about securing and bolstering your current network and cyber security with one of our cyber security and network protection service accounts.
Workstation and Server Deployment
When it comes to the roll out of large quantities of PC’s and Servers, Atlanta I.T. Service is the proven choice offering exponentially more efficient service than anyone else.
From time to time, certain situations require special attention. Atlanta I.T. Service offers priority service to customers who have special needs.
If you have or need remote offices, Atlanta I.T. Service can design, implement, and support the optimal Wide Area Network for your business.
We offer highly reliable, automated backups and recovery services that assure fast and accurate restoration following data loss or destruction.
We are a Georgia State Low Voltage Licensed Contractor. Low voltage cabling is the backbone of most networks and telecommunication infrastructures.
Your organization deserves to put its best foot forward on the internet. Let us assess your needs and provide dynamic, memorable and tasteful web designs.
We pride ourselves on making sure you get the most comprehensive experience possible.
Recent News
-
Microsoft Issues Emergency Windows Security Update For A Critical Vulnerability
If your computer is running Microsoft’s Windows operating system, then you need to apply this emergency patch immediately. By immediately, I mean now!Microsoft has just released an emergency security patch to address a critical remote code execution (…
-
Security Flaw Leaves Major Banking Apps Vulnerable to MiTM Attacks Over SSL
A team of security researchers has discovered a critical implementation flaw in major mobile banking applications that could leave banking credentials of millions of users vulnerable to hackers. The vulnerability was discovered by researchers of the Security and Privacy Group at the University of Birmingham, who tested hundreds of different banking apps—both iOS and Android—and […]
-
Young Hacker, Who Took Over Jail Network to Get Friend Released Early, Faces Prison
Well, “a friend in need is a friend indeed” goes a long way, but in this case, this phrase hardly makes any sense.A 27-year-old Michigan man who hacked into the government computer system of Washtenaw County Jail to alter inmate records and gain early…
-
Forever 21 Warns Shoppers of Payment Card Breach at Some Stores
Another day, another data breach. This time a fast-fashion retailer has fallen victim to payment card breach.American clothes retailer Forever 21 announced on Tuesday that the company had suffered a security breach that allowed unknown hackers to gain…
-
2.5 Million More Americans Were Affected By Equifax Breach
The Equifax data breach was bigger than reported, exposing highly sensitive information of more Americans than initially revealed. According to Credit rating agency Equifax an additional 2.5 million U.S. consumers were impacted by the massive data breach, the company disclosed last month, bringing the total possible victims to 145.5 million from 143 million. Equifax last […]
-
CCleaner Malware uses Secondary Backdoor to Infect Tech Companies
A group of unknown hackers, which hijacked CCleaner’s download server to distribute a malicious version of the system optimization software, targeted at least 20 major international technology companies with a secondary payload. Beginning of this week, when the hack was reported, researchers assured users that there’s no second stage malware used in the massive attack […]
-
New Email Campaign Sends Locky Ransomware to Millions of Users
Researchers from two security firms have independently spotted two mass email campaigns, spreading two different, but new variants of the Locky ransomware. Lukitus Campaign: Sends 23 Million Emails in 24 Hours The campaign found by researchers at AppRiver sent out more than 23 million messages containing the Locky ransomware, in just 24 hours on 28 […]
-
Millions of Email Addresses Exposed From SpamBot Server
A massive database of over 630 million email addresses used by a spambot to send large amounts of spam to has been published online in what appears to be one of the biggest data dumps of its kind. A French security researcher, who uses the online name Benkow, has spotted the database on an “open […]
-
Hackers Hijack Chrome Extension to Push Malware
Recently an extension for Google Chrome has been hacked, after compromising the Chrome Web Store account of a German developer team from a9t9 GmbH, and abused it to distribute spam messages to unsuspecting users. Named Copyfish, the extension allows users to extract text from images, PDF documents and video, and has more than 37,500 users. […]
-
The way Hackers Cash Out Thousands of Bitcoins Received in Ransomware Attacks
Digital currencies have emerged as a favorite method of payment, not only for regular folks, but also for hackers and cyber criminals, as digital currency transactions are nearly anonymous, allowing cyber criminals to use it in underground markets for illegal trading, and to receive thousands of dollars in ransomware attacks—WannaCry, Petya, LeakerLocker, Locky and Cerber […]
-
Microsoft Workplace Analytics
SoftwareMicrosoft Workplace Analytics Microsoft Just released a new monitoring tool, that allows company leaders to see how teams within their organization spend their time. The brand-new program, Microsoft Workplace Analytics is available for purchase as an add-on to the Office 365 Enterprise plans. According to the director of Microsoft Office 365, Alymn Rayani, ” the […]
-
New Petya Ramsom classified as Wiper Malware
The Petya ransomware attacks that has spread in several countries, including Russia, Ukraine, France, India and the United States on Tuesday, and demands $300 ransom, was not created with the purpose of restoring infected computers at all. Comae Technologies Founder Matt Suiche, who closely looked at the operation of the malware, said after analyzing the […]