Our Services
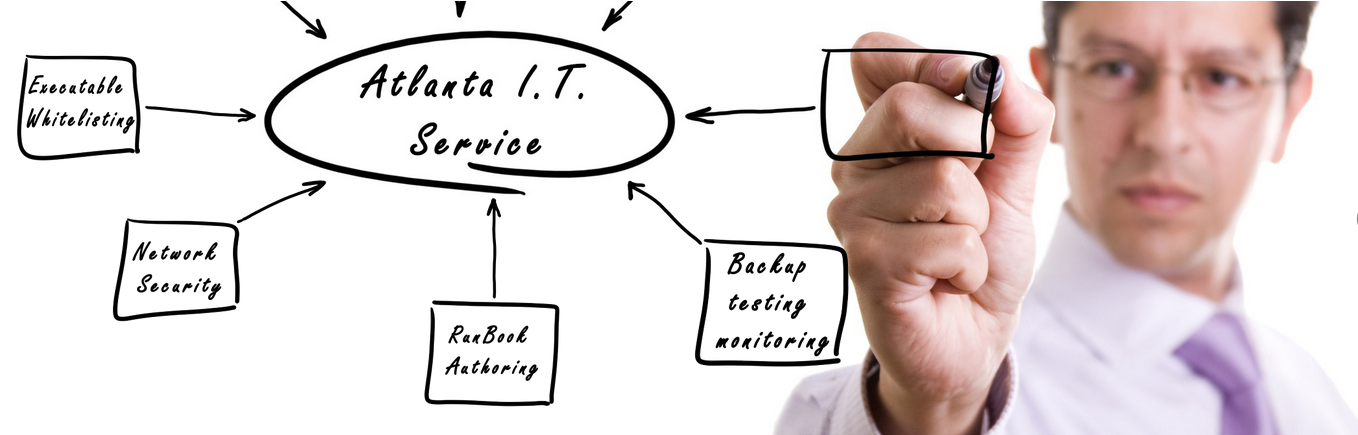
If your business is dependent on the data that it generates from day to day, you should consider speaking with us about securing and bolstering your current network and cyber security with one of our cyber security and network protection service accounts.
Workstation and Server Deployment
When it comes to the roll out of large quantities of PC’s and Servers, Atlanta I.T. Service is the proven choice offering exponentially more efficient service than anyone else.
From time to time, certain situations require special attention. Atlanta I.T. Service offers priority service to customers who have special needs.
If you have or need remote offices, Atlanta I.T. Service can design, implement, and support the optimal Wide Area Network for your business.
We offer highly reliable, automated backups and recovery services that assure fast and accurate restoration following data loss or destruction.
We are a Georgia State Low Voltage Licensed Contractor. Low voltage cabling is the backbone of most networks and telecommunication infrastructures.
Your organization deserves to put its best foot forward on the internet. Let us assess your needs and provide dynamic, memorable and tasteful web designs.
We pride ourselves on making sure you get the most comprehensive experience possible.
Recent News
-
Web Browsers implementation of DNS over HTTPS TLS
Immediately after Mozilla announced its plan to soon enable ‘DNS over HTTPS’ (DoH) by default for Firefox users in the United States, Google today says it is planning an experiment with the privacy-focused technology in its upcoming Chrome 78. Under development since 2017, ‘DNS over HTTPS’ performs DNS lookups—finding the server IP address of a […]
-
Step by step guide to repair damage from McAfee Intel VirusScan Enterprise 9226 Dat
On April 13th 2019 McAfee and Intel release a definition update DAT Version 9226 and another one on April 14 DAT Version 9227 and they did a lot of damage very quickly to many computers. If you look at your Quarantine Manager you will find numerous entries for RDN/ScreenConnect. When you right click these and […]
-
Using Compromised Passwords and information
Lots of changes are happening all around us on a daily basis when it comes to today’s technological conveniences. Many of us do not have an interest in news about businesses that have become compromised or sometimes even government agencies. This list of organizations is incredibly long and has a direct effect on billions of […]
-
Is your staff equipped to use company email without being a threat?
Is your staff equipped to use company email without being a threat? Google subsidiary Jigsaw recently put that question to many of us through this simple online simulation quiz. We highly recommend if your company is not enrolled in any Phishing education programs to encourage your staff to take this simple, safe and fast quiz […]
-
New malware found using Google Drive as its command-and-control server
Since most security tools also keep an eye on the network traffic to detect malicious IP addresses, attackers are increasingly adopting infrastructure of legitimate services in their attacks to hide their malicious activities. Cybersecurity researchers have now spotted a new malware attack campaign linked to the notorious DarkHydrus APT group that uses Google Drive as […]
-
Malware Gets Commands From Memes Posted On Twitter
Security researchers have discovered yet another example of how cybercriminals disguise their malware activities as regular traffic by using legitimate cloud-based services. Trend Micro researchers have uncovered a new piece of malware that retrieves commands from memes posted on a Twitter account controlled by the attackers. Most malware relies on communication with their command-and-control server […]
-
FBI Seizes 15 DDoS-For-Hire Websites, 3 Operators Charged
The U.S. Justice Department announced earlier today that the FBI has seized domains of 15 “DDoS-for-hire” websites and charged three individuals running some of these services. DDoS-for-hire, or “Booter” or “Stresser,” services rent out access to a network of infected devices, which then can be used by anyone, even the least tech-savvy individual, to launch […]
-
Hacker Discloses New Unpatched Windows Zero-Day Exploit On Twitter
A security researcher with Twitter alias SandboxEscaper today released proof-of-concept (PoC) exploit for a new zero-day vulnerability affecting Microsoft’s Windows operating system. SandboxEscaper is the same researcher who previously publicly dropped exploits for two Windows zero-day vulnerabilities, leaving all Windows users vulnerable to the hackers until Microsoft patched them. The newly disclosed unpatched Windows zero-day […]
-
Hacking Team Spyware preloaded with UEFI BIOS Rootkit to Hide Itself
Last Week someone just hacked the infamous Hacking Team, The Italy-based cyber weapons manufacturer and leaked a huge trove of 400GB internal data, including: Emails, Hacking tools, Zero-day exploits, Surveillance tools, Source code for Spyware and A spreadsheet listing every government client with date of purchase and amount paid. Hacking Team is known for its […]
-
Ex-NSA Developer Gets 5.5 Years in Prison for Taking Top Secret Documents Home
A former NSA employee has been sentenced to five and a half years in prison for illegally taking a copy of highly classified documents and hacking tools to his home computer between 2010 and 2015, which were later stolen by Russian hackers. Nghia Hoang Pho, 68, of Ellicott City, Maryland—who worked as a developer with […]
-
How to Hack WiFi Password Easily Using New Attack On WPA/WPA2
Looking for how to hack WiFi password OR WiFi hacking software? Well, a security researcher has revealed a new WiFi hacking technique that makes it easier for hackers to crack WiFi passwords of most modern routers. Discovered by the lead developer of the popular password-cracking tool Hashcat, Jens ‘Atom’ Steube, the new WiFi hack works explicitly […]
-
SUSE Linux Has Been Sold For $2.5 Billion
SUSE, the open source software company owned by British firm Micro Focus International, has been sold to a Swedish private equity firm. Yes, SUSE Linux and its associated software business has finally been acquired by EQT Partners for $2.535 billion, lifting its shares 6 percent. SUSE is one of the oldest open source companies and […]