Short Password Reset code vulnerability allows hackers to brute-force many websites
Yesterday we received a vulnerability report in web applications from some unknown Indian Hacker, who explained that how Hackers are hijacking Mobile recharge and Free SMS service related websites.
He detailed the loophole in password reset process, that could allow attackers to brute force many high profile websites that are actually not protected by the image CAPTCHA verification system, during the password reset process.
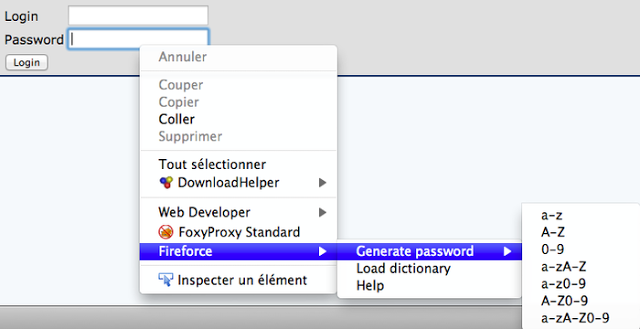
The hacker used a Firefox Browser equipped with the Fireforce add-on, a very simple a Firefox extension designed to perform brute-force attacks on GET and POST forms.
The technique proposed by him targets the unsecure password reset process used by many websites, where the web application used to send a code to the user’s mobile or email for authenticity verification.
Around 40% websites adopts password reset code composed of numbers and of some fixed length, typically having a length less than 5 digits.
This information could advantage attackers in the password cracking process, the first thing to do is to request a password reset code and then try to attack the password reset code page with Fireforce add-on.
After a successfully hack it is possible to reset the password of the victim, the brute force attack is in reality not so complicated under the above conditions, an attacker has to test only some 1000-100000 passwords based on code length.
There is also another procedure that could improve the cracking process and make it faster. Typically a password reset code never starts with 0, this condition could be used by the attacker to refine the search.
The attacker could edit the Fireforce script so that it starts the attack from 1***** testing at the end of cracking process the combinations having following format 0*****.
To edit the Fireforce script download the fireforce.xpi file as shown in the following picture:
Then open the Fireforce.xpi file using Winrar or any similar application searching for a file named “fireforce_generatePassword.js”, just modifying the string
“case “0-9” : char = “0123456789” to “case “0-9” :char = “1234567890”;
It is possible to decide the sequence of tries for the brute force attack. Save the file to fireforce.xpi archive and Open the file with Firefox and install it.
At this point the attacker could hit any webpage he want that is not protected. Generally free Sms sites are vulnerable to this kind of attack because they send a string of numbers as their verification code to the user’s mobile.
Latest Hacking News Updates
Author details
Pierluigi Paganini is Company Director, Researcher, Security Evangelist, Security Analyst and Freelance Writer. Security expert with over 20 years experience in the field. The passion for writing and a strong belief that security is founded on sharing and awareness led me to found the security blog ‘Security Affairs’ He is also Author of the book “The Deep Dark Web”. Follow him @ Facebook | Google | Email | Twitter
![]()
